Business Sectors
Events
Contents
Register to read more articles.

Complete cyber risk assessments to safeguard ships
Six months on from the enforcement of IMO’s cyber risk management regulations, shipping companies are implementing cyber security across their fleets – but there are challenges ahead and issues to overcome
Experts in cyber risk management and their associated regulations outlined the key challenges during Riviera Maritime Media’s Cyber risk management in safety management systems – six months on webinar.
This event was held on 10 June 2021 as the second webinar of Riviera’s Maritime Cyber Tech & Ops Webinar Day.
A distinguished panel included Danish Maritime Authority special adviser Erik Tvedt, who helped write key IMO cyber risk management regulations. He was joined by BIMCO head of maritime safety and security Jakob Larsen and CyberOwl chief executive and cyber security expert Daniel Ng.
They outlined how shipping companies and managers had adapted to new regulations brought into force by IMO in January this year to implement cyber risk management in the International Shipmanagement (ISM) Code.
Mr Tvedt explained the main changes in regulations.* “We needed a regulatory framework to follow what comes out of IMO and the EU,” said Mr Tvedt, “for the safety and navigation of ships”.
For the Danish Maritime Authority (DMA), ship safety was the most important focus of adopting regulations. It takes into account the effect of any cyber risk on networks and information systems, and whether a cyber incident would have significant disruptive effects on ships and their navigation.
“For example, on the operating technology, supervisory control and data acquisition controls the engines, electronic controls, ECDIS and safety critical communications,” said Mr Tvedt.
DMA is monitoring whether classification societies and other recognised organisation are auditing cargo ships under Danish flag and will audit all passenger ships and special cases.
In his presentation, Mr Tvedt provided some insights into the lessons already learned by the shipping industry and DMA from previous cyber incidents and implementing IMO 2021 regulations thus far. This included issues with software and deploying internet of things (IoT) on ship operational technology (OT).
“Software quality and systems integration is by far the biggest problem as seen from a safety point of view – it is a far bigger problem than hackers,” said Mr Tvedt.
“There have been a lot of issues, headaches and problems with software quality. It is good to have cyber risk management, and maintain and run safety critical software systems.”
Some of the biggest issues come from shipping companies trying to retrofit existing onboard systems for IoT applications.
“Built-on data collection is a major headache,” Mr Tvedt continued. “It compromises systems that would have otherwise been perfectly safe. Old OT systems are best left alone.”
He warned shipping companies not to just accept solutions from IT departments and update OT. “Do not compromise. If you want an integrated data-collating system, do not use existing systems – go get something new and keep it air-gapped,” said Mr Tvedt.
He said other challenges come from vendors installing their IoT systems on OT.
“When doing an update, treat this as hot work and never do it at sea,” he warned. “Do not update software when a ship is sailing as this could compromise the safety of the ship. Keep the OT safe, avoid tampering and make sure no one else can break something.”
This viewpoint resonated with webinar attendees who were asked their opinions through poll questions. Of those who responded, 40% had experienced software malfunctions not related to cyber attacks on their ships that had a significant disruptive effect on ship safety. The other 60% had not.
But very few had experienced cyber-related incidents. When asked had they experienced cyber attacks on vessels that had significant disruptive effects on ship safety, 95% voted no and just 5% yes.
BIMCO’s Mr Larsen had sympathy for the 5% that had, as he was involved in Maersk’s recovery after a devastating cyber attack 1n 2017, which cost more than US$200M to rectify. He said Maersk was only saved from complete data loss by an accidental power outage in Nigeria that prevented the ransom malware from destroying information on a back-up there. That cyber attack was damaging to Maersk Line’s commercial business and disrupting to terminal operations, but did not affect container ship safety.
Mr Larsen said ransomware was outside the scope of IMO resolution MSC.428(98) and ISM regulation. “But there are safety issues,” he said.
“Safety management objectives of shipping companies should assess all identified risks to its ships, personnel and the environment and establish appropriate safeguards.”
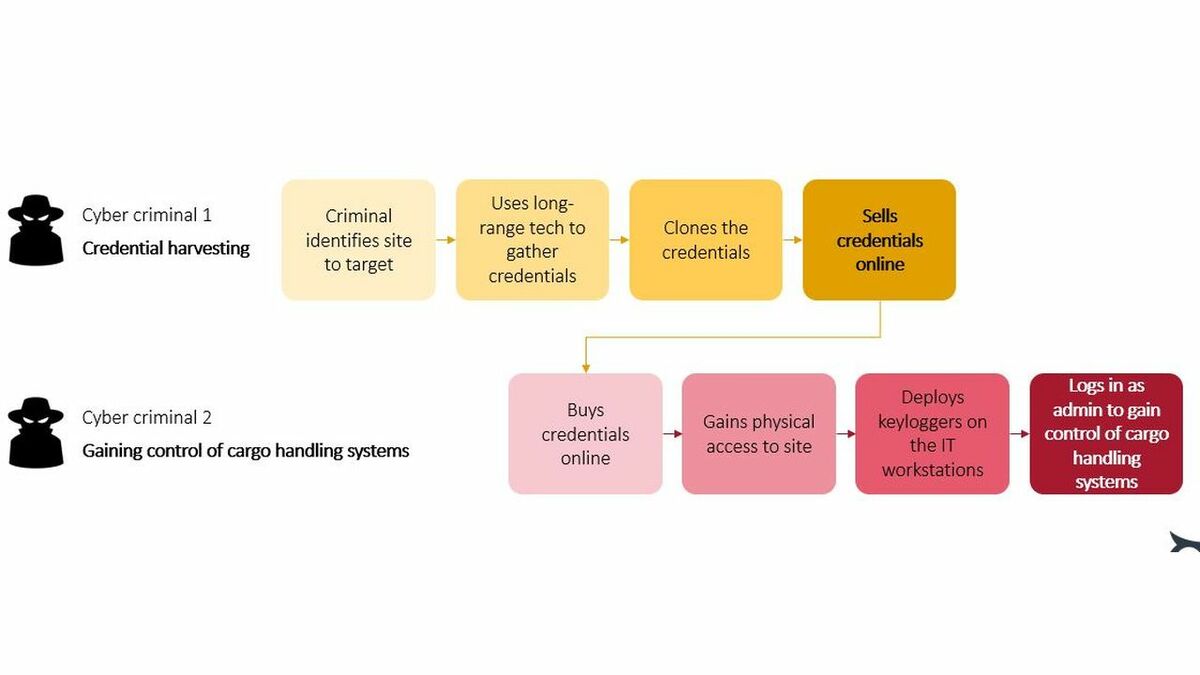
He suggested one risk to ship safety could be hackers changing container manifests to allow banned or hazardous materials on board ships without a master’s knowledge.
These could be included in a shipping company’s cyber risk management, as could so many other issues, vulnerabilities and threats.
Mr Larsen suggested part of the risk assessment should be the likelihood of its occurrence, the impact if it happens and the opportunity hackers have to implement that risk.
“You need to include probabilities, as it can be expensive to protect against every risk,” he said. “Ships are open, so there are plenty of opportunities, but do hackers have intent to go after a ship, or something else? It is important to look at the full picture,” Mr Larsen commented.
He recommended shipping companies use safety management system matrices to assess risks and to communicate these to senior management.
They should map remote access and data flows, segregate networks by separating critical systems from administration, crew and passenger networks, and protect access to shipboard computers and systems.
This includes firewalls, password management, dealing with removable media ports and physical access control. Email and other internet-facing systems and software also need to be protected using antivirus programs and all staff trained.
“Protect ships, especially when there have been updates to IT, and if there are overlaps between networks as these are the real threats,” said Mr Larsen.
“Changes in IT means keeping risk assessments up-to-date is key. Going forward these challenges will become bigger as ships become more connected.”
Other challenges will come from deciphering the exposure of OT to cyber risks and lack of visibility to online threats, according to delegates.
When they were asked what their biggest cyber risk blindspots were, 48% voted for understanding the actual exposures of OT systems. Another 33% said it was not having continuous visibility of cyber risks and 19% thought it was reliability of cyber risk assessments. None voted for accuracy of inventory of on board systems nor there were no significant blindspots.
CyberOwl’s Mr Ng thought there were several blindspots and issues shipping companies face in implementing cyber security. His company has surveyed hundreds of fleet operators and collated observations from ships it monitors.
Initial findings from the study show fleet operators do not fully trust their cyber risk assessments and are struggling to “identify vulnerabilities, understand likelihoods and impacts” said Mr Ng. “It is not practical to secure everything,” he added, “But it is about securing the crown jewels, the operations and safety that are linked to how vulnerabilities are attacked.”
A key issue is the lack of data illustrating likelihoods and impacts from a cyber attack on ship safety. “Risk assessments are still theoretical and desktop based – they are not based on physical evidence,” said Mr Ng. So, shipping companies are “not getting the ability to prioritise”, which has “implications to shipping and insurance”.
Key inputs into a typical risk assessment are network architecture diagrams, documentation from vendors, interviews of internal stakeholders and physical surveys by safety experts, not necessarily by IT experts.
Mr Ng said the top five weakest assumptions in a typical cyber-risk assessment are architecture diagram accuracy, inventory inaccuracy, separated networks, good control over internet-facing systems and control over the use of memory sticks via physical locks.
“Often bolt-on systems are not well understood and tend to be back doors to incidents,” said Mr Ng. “Not all networks are separated, and this creates vulnerabilities – you cannot view OT in isolation.
“Time and again, what is expected in controls is not being implemented over a fleet of vessels.” This is especially the case after onboard networks have been updated.
“We detect one new cyber event every day over the fleet we monitor,” commented Mr Ng. “80% relate back to unauthorised programs installed on business-critical computers.”
This happens when crew or visitors on vessels need to do something operational, such as download or upload something onto OT/IT, or update software.
Coming back to Mr Tvedt’s point, Mr Ng said “unauthorised and bad software were the biggest issues observed”.
But at least, of the around 200 cyber incidents observed so far in 2021, all were level one only.
There were no safety impacts and no damage to ships, because good response plans were in place. “It is good to keep everything at level 1,” said Mr Ng.
After hearing from these experts, webinar attendees were asked what their vessel cyber security priorities were for the next 12 months. Of those responding, 56% said to complete cyber-risk assessments, 31% thought to identify and implement cyber controls, 7% said selecting and deploying cyber-security technology and 6% voted for something else.
*Regulations include IMO resolution MSC.428(98) for including cyber risk management in safety management systems and European Parliament and Council directive 2016/1148/EU, concerning measures for a high common level of security of network and information systems across the European Union (NIS Directive)
On Riviera’s Cyber risk management in safety management systems - six months on webinar webinar panel were (left to right): BIMCO head of maritime safety and security Jakob Larsen, Danish Maritime Authority special adviser Erik Tvedt and CyberOwl chief executive and cyber security expert Daniel Ng
Related to this Story
Events
Maritime Cyber Security Webinar Week
Marine Propulsion: Fuels Webinar Week
How enhanced connectivity is propelling maritime into the AI era
Marine Lubricants Webinar Week
© 2023 Riviera Maritime Media Ltd.