Business Sectors
Events
Contents
Cyber security: defending the tanker at sea, in port and from the crew
There are two levels of maritime security: that required for regulatory requirements and that necessary to meet threats that occur during a voyage, at a terminal, and from the human factor
Discussing IMO resolution MSC.428(98), and the requirement that all shipboard safety management systems be documented as having included cyber-risk management no later than a vessel’s first annual Document of Compliance audit in 2021, Inmarsat Maritime’s retail director Laurie Eve offered an overview of the IMO 2021 guidance.
Owners, Mr Eve said, should be in no doubt that they will face enforcement of the guidance by port state control authorities such as the US Coast Guard. “Ships could be detained and owners fined for noncompliance,” he said. “Shipowners need to demonstrate they have considered the risk and what to do if there are issues."
Ships should have certification and documentation, but compliance with IMO 2021’s cyber guidelines requires owners to understand each vessel’s cyber risk. “There is no silver bullet, no definitive checklist,” said Mr Eve. “It depends on a ship’s cyber risk, so [owners and managers] need to have a risk management approach.”
CyberOwl’s Daniel Ng explained how his company’s recent survey of 50 fleet operators found good implementation of some of IMO 2021 requirements and cyber-risk management. He said owners, operators and managers had started training employees and set up “aspects of emergency plans” but much still remained to be done. “They are still struggling at incident readiness and are not monitoring for attacks on shipboard systems,” Mr Ng said.
A worrying issue is the number of onboard systems still connected to vessel satellite communications. “Operational technology (OT) should be air-gapped but are unknowingly connected to the vessel business network,” he said. These include loading computers, closed-circuit television systems and engine monitoring and alarm systems.
“These are critical systems, with loading computers linked to the ballast system for example,” Mr Ng said. “Controls need to be in place. Engine monitoring systems should be air gapped.”
CyberOwl also examined shipboard computers, looking for unwanted and potentially dangerous programs, which are regularly installed. “The top offender is PDF editing software,” according to Mr Ng: “In shipping there are a lot of documents and often they come in PDF format and need to be edited and sent back to offices.” If owners have not installed official software for PDF editing, crew will seek to upload free and potentially hazardous programs, “just for the job they need to do” said Mr Ng.
“Plan for the inevitable. It will happen”
Other unwanted programs found in onboard computers include gaming, image editing and messaging software. “These do not have levels of security and could be back-doors for malware,” he said.
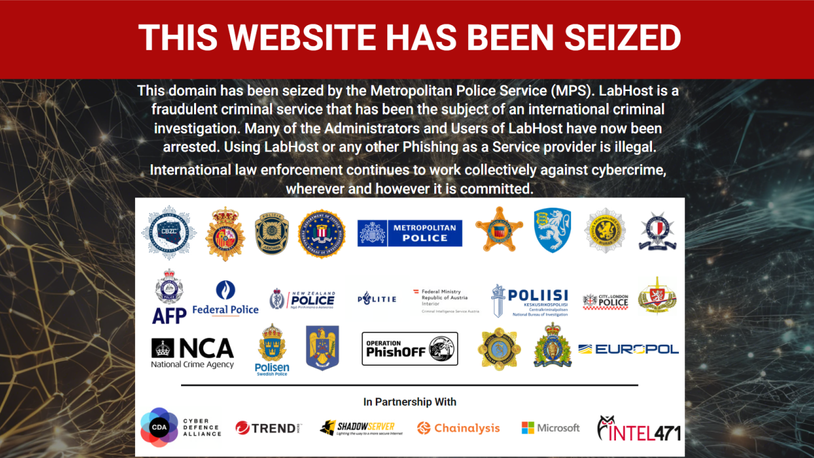
University of Piraeus cyber security associate professor Nineta Polemi noted the importance of collaboration across the supply chain in order to strengthen cyber security for all involved. “There are a plethora of partners and assets, so how can we secure all these supply chain services?” she asked. “It is difficult to estimate and mitigate supply chain risk and difficult to respond if there is a cyber-attack propagating through the supply chain."
Ms Polemi called on regulators, such as IMO and the European Union, to collaborate on guidance and compliance requirements. “It is challenging to enhance collaboration and to share threat intelligence and incident handling,” she said.
In a survey, 28% thought the biggest challenge to cyber security was OT and internet-of-things (IoT) networks, with 25% thinking it was operational challenges. Another 19% said personnel, with 13% citing costs, 6% administration, 6% installation and just 3% highlighting the need to identify the right software.
There was also a very low level of preparedness for IMO 2021 cyber security requirements. Only 11% said they were completely ready and 5% thought they had not started. Some 12% said they were 10% ready, 14% said they were a quarter along the way, 40% said they were halfway prepared and 18% said they were 75% prepared.

Most in the survey (28%) confessed to being poorly prepared to identify a cyber risk in good time. Cyber training was a huge gap for many respondents: 35% said training had never been done; another 23% said it was, but more than a year ago; 16% said it was conducted 6-12 months ago; and 26% said in the past six months.
The lack of preparedness among seafarers is understandable, given the responsibilities at sea, but ports seem to be equally unprepared. In a survey, only a third thought there were cyber security guides for port stakeholders, and 67% thought there was no awareness. A worrying 64% believed that there had already been a cyber attack on a port.
University of Plymouth research fellow for cyber security Dr Kemedi Moara-Nkwe noted that cyber-attacks on logistics hubs would devastate the supply chain network with tremendous financial damage. He said cyber threats could affect OT such as supervisory control and data acquisition (SCADA) systems and IT networks in ports. “Ports are unique in their interfaces between IT and OT, such as for cargo loading and unloading,” he said. He noted a cyber-attack initiated in IT could impact substations, electrical systems and automated cranes. “Ports depend on the technology and need to consider the risks as a cyber-attack can affect availability of technology and assets,” said Mr Moara-Nkwe.
Norway has taken a proactive step in establishing the Norwegian Maritime Cyber Resilience Centre (NORMA) for building unified resilience against cyber threats. NORMA’s cyber managing director Lars Benjamin Vold said: “New technology has been developed for cyber-defence purposes, while existing structures and organisations can be built on.” NORMA provides an intelligence- and information-sharing service and an incident response and crisis support service. “From 1 June 2021, we will be a security operations centre, with services tailored for the shipping and maritime sector,” said Mr Vold.
McDermott Will & Emery partner Paul Ferrillo noted that in the US, the Coast Guard was the chief maritime law enforcement agency. He said the national maritime cyber security plan “rides side-by-side with the US Coast Guard’s guidelines for addressing cyber risks” at Maritime Transportation Security Act (MTSA)-regulated facilities (NVIC). “[This] generally requires these ports to address and document network and cyber security vulnerabilities,” said Mr Ferrillo. MTSA requirements are mandatory, while the US Coast Guard’s NVIC is guidance for reminding port facilities of the need to comply with MTSA regulations.
“Controls need to be in place; engine monitoring systems should be air gapped”
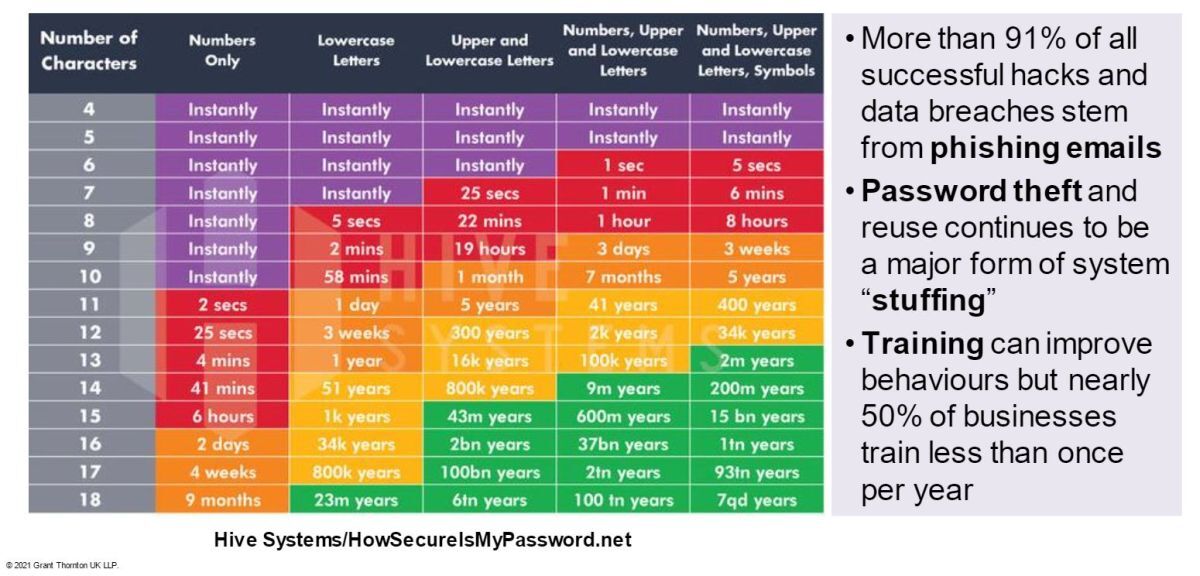
Having regulations in place is one thing, but ultimately, cyber security is a personal and personnel issue. People are the weakest link hackers can use to unpick company network security. Grant Thornton, UK partner for digital forensic group Vijay Rathour said: “Attackers have time and motivation to penetrate your systems. Malware and phishing continue to be leading forms of system penetration, typically through social engineering.”
Mr Rathour said shipping companies need to plan for cyber-attacks and ensure they can recover. “Plan for the inevitable. It will happen,” he said. “Know how to recover, train and make sure it does not happen again.”
Inmarsat senior vice president for global cyber security Graham Wright said that Inmarsat had implemented high levels of cyber security and personnel training to prevent billions of penetration attempts from getting through. “There are around 50Bn events on our internal systems every month,” he said.
Wärtsilä Voyage head of cyber security and technology Paivi Brunou said cyber security was everyone’s responsibility and that there needs to be more awareness of the threats and their consequences. “It is all-hands-on-deck for cyber security,” she said. People need to be aware of how their errors of judgement can lead to cyber-attacks. “80% of cyber-attacks are not from malicious attacks, but from mistakes we make,” said Ms Brunou.
Wilhelmsen Group director of security, governance, risk management and compliance Morten Drægni agreed, using the analogy of a cupcake on the floor being like a discarded USB storage device. Mr Drægni said people would not consider picking up and eating the cupcake, but they do pick up USBs and plug them into their computers to view what is on them. “It is important to increase safety culture,” he said. “It is not just a tick-off for compliance. It is about improving cyber security, sharing information, learning from mistakes and working together.”
But according to a survey, cyber security and safety training remains a low priority. When asked about cyber-security awareness programmes in their organisations, 46% said it was once a year, 44% said it was a continuous focus of the company and 10% thought it was two to four times a year. Practical guidance was low-key; in a survey, 18% said they had participated in cyber-security related table-top exercises, drills or simulations within the past 12 months, with 82% saying they had not.
Five actions to increase a vessel’s cyber security
Russian Maritime Register of Shipping (RS) makes the following recommendations when it comes to marine cyber security. First of all, and most important for a shipowner, is to realise that cyber-security risks are absolutely real. No vessel may be considered protected from cyber threats without a relevant analysis and an assessment of the results. Even an old ship that lacks computerised automation systems for propulsion, cargo-handling operations, etc may be vulnerable, bearing in mind there are ECDIS, AIS and other onboard equipment made compulsory under international conventions.
Therefore, the shipowner is recommended to:
(1) Assess the cyber-attack and cyber-incident risks to provide uninterrupted service of its shore-based divisions and ships in compliance with SMS risk assessment procedures and identify vulnerable data and resources and risk mitigation measures.
(2) Provide adequate resources (time, human resources, financial) for the implementation of the measures identified.
(3) Define personnel solutions on cyber-security management and embed cyber-risk awareness culture at all levels, including top management, through relevant training.
(4) Develop specific measures for cyber-attack detection, response, consequence minimisation and recovery of the attacked objects and system operability.
(5) Periodically verify and assess the entire cyber-security management system.
In order to assist stakeholders, mitigate ship cyber-attack vulnerability and help implement IMO Resolution MSC.428(98), RS has published Guidelines on Cyber Safety. The document provides recommendations on the design, manufacture, maintenance and testing of shipboard computer-based systems, as well as recommendations applicable to the safety management systems.
Related to this Story
Events
Maritime Cyber Security Webinar Week
International Chemical & Product Tanker Conference 2024
Marine Propulsion: Fuels Webinar Week
How enhanced connectivity is propelling maritime into the AI era
© 2023 Riviera Maritime Media Ltd.