Business Sectors
Events
Contents

How to keep satcoms cyber secure
While developments in satcoms technology undoubtedly bring great benefits, the always-on connection can make vessels more vulnerable to cyber risks
Digitalisation of the maritime sector is continuing apace, and everyone from deck crew to the board of directors feels the benefits of increased connectivity in areas ranging from equipment maintenance, fuel consumption, navigation, crew welfare and more, with the subsequent positive effects these have on a company’s costs.
However, we do not need to look far for a painful reminder that as more attention is devoted to connectivity and the efficiencies and benefits it brings, these must be safeguarded by a proactive approach to cyber security.
This was illustrated in 2017, when AP Møller-Maersk fell victim to the NotPetya ransomware attack, with an estimated cost to the company of US$300M due to the attack's impact on co-ordinating the company’s operations at terminals and ports around the world. Over the course of 10 days in June and July 2017, Maersk’s IT staff reinstalled more than 4,000 servers, 45,000 PCs and 2,500 applications as part of the recovery effort. It is also worth noting that this was not believed to be a targeted attack – Maersk chairman Jim Hagemann Snabe said in the aftermath he believed the company was “collateral damage of probably a state attack.”
And in the years since, the cyber threat has only grown. Research from Finland-based cyber security provider F-Secure released in March 2019 reported a significant increase in traffic during 2018, with a fourfold increase in the second half of the year compared with the first half.
What is a cyber threat?
Attacks can be targeted, with a particular goal in mind, or they may be untargeted, such as ransomware attacks, which encrypt a victim’s files and demand a cryptocurrency payment be made before they are released.
Once an attacker has breached a ship’s defences, its location, route and other sensitive information such as cargo details can be accessed.
Speaking at a digitalisation conference in Singapore in November 2018, KPMG’s director of cyber security practice Dr Paul Lothian noted that the kind of sensitive information attackers will target could include cargo manifests, operational information such as system configurations and voyage data, and HR information such as personal employee and payroll details.
And it is not only on the balance sheet that a cyber attack will be felt. While so far maritime cyber attacks have resulted in lost money and time, there is also potential for physical harm to equipment or even personnel.
Cruise vessels have an even greater need for security, carrying large numbers of passengers, many of whom will expect wireless connectivity on board.
Where is it coming from?
In 2019 threats can come from a range of actors. Increasingly, cyber threats come from sophisticated groups, sometimes with nation-state backing. In its November 2018 report on the current and anticipated future cyber threat, California-based analysts and cyber security company FireEye highlighted several areas to keep an eye on.
One such example is a group known as TEMP.Periscope, which focuses on areas such as defence, shipping, manufacturing and government institutions in the US, western Europe and along the South China Sea.
FireEye’s analysis of this group notes activity believed to be consistent with its methods “likely reflects a concerted effort to target sectors that may yield information that could provide an economic advantage, research and development data, intellectual property, or an edge in commercial negotiations.
As well as potentially interfering with vessel operations, such attacks can seek to gain access to sensitive data relating to employees, company financials or operational technology.
As China’s Belt and Road initiative (BRI) develops a land and maritime trade network, FireEye anticipates a growth in cyber threat activity. This is likely to include emerging groups and nation-state actors.
“Given the range of geopolitical interests affected by this endeavour, it may be a catalyst for emerging nation-state cyber actors to use their capabilities.
Regional governments along these trade routes will likely be targets of espionage campaigns," says FireEye in the report.
“Media announcements on BRI progress, newly signed agreements, and related development conferences will likely serve as operational drivers and provide lure material for future intrusions.”
What can be done?
One option for vessel owners and operators seeking to establish exactly how vulnerable they could be to attack is penetration testing. Pen Test Partners is a company that specialises in such risk assessments and has highlighted the potential status of satellite terminals as a weak link in the cyber security chain.
Pen Test Partners noted that the satellite communications vulnerabilities they have highlighted can be resolved simply by setting a strong admin password, as recommended by manufacturers. PenTest partners also suggest moving to a private connection, so that your box is not visible on the public internet, is a wise move. Another recommendation is that firmware on terminals is kept updated to the most recent version.
Indeed, while it may be difficult to co-ordinate keeping systems patched and up-to-date across an entire fleet of vessels, this is a step toward more efficient cyber security that costs nothing. In the case of the NotPetya attack, the vulnerability the malware took advantage of was an unpatched Microsoft Windows operating system.
The human element is also key to cyber security. KPMG’s Dr Lothian noted in his presentation that a survey had found only 12% of crew had undergone any form of maritime cyber security training, which he noted was well below industry averages.
Inmarsat Maritime senior vice president of safety and security Peter Broadhurst says “Many attempts to gain unauthorised access to IT infrastructure require some sort of activation by an end-user to infect a system and cause further damage.
“These attacks are often heavily disguised so as to trick and manipulate end-users into unwittingly granting permission.
“However, there are nearly always tell-tale signs that, if spotted in time, would prevent escalation. Crew education is therefore an indispensable component in realising a well-rounded security strategy.”
Policies can be surprisingly straightforward in this area. Zodiac Maritime has previously told Maritime Digitalisation & Communications it forbids crew members bringing USB memory sticks or devices onto the bridges of vessels it manages, including to update the ECDIS system. Instead, updates are carried out using CDs or over a secure internet link using VSAT, or if these are not available, by using a trusted local supplier.
Crews may bring their own devices such as laptops, smartphones and thumb drives on board vessels, and connect them to the ship’s network. This brings challenges to cyber security as it can result in a more porous network perimeter, with each device connected to the network a potential entry point for security risks such as malware.
Endpoint security focuses on these network nodes, comprising a central system installed on the network and client software on each endpoint device that uses systems such as encryption and application control to bolster security. Inmarsat’s Fleet Secure Endpoint is an example with features such as a two-way firewall, botnet and ransomware protection, network monitoring, and health status and threat alerting.
Network separation is also an important consideration and can help to prevent attacks spreading to business- or operations-critical systems.
VSAT provider KVH promotes a six-level approach to cyber security at different strategic levels, including seafarer training, satellite network security, terrestrial network security, hardware and network configuration security, protected internet egress, and a dedicated cyber security incident response team. This means onboard local area networks can be configured for segmentation into operations, crew networks and third-party charter networks.
KVH vice president of satellite products and services Rick Driscoll says “To enhance the security of transmissions between ship and shore, we have designed our system so that traffic does not touch the internet before going through edge security devices at MegaPOP [point of presence access point – an interface between communicating entities].”
It is clear there are a number of areas where cyber security can be improved. As Dr Lothian has pointed out, cyber security is not a one-and-done solution – it is a constant, ongoing process. New threats are constantly evolving, and defences are being breached. The only way to counter this is as an organisation is to have an adaptive cyber security policy that everyone is aware of and follows.
How are VSAT systems vulnerable?
Using penetration testing, a risk assessment method that simulates an attack on an asset or company, vulnerabilities in VSAT terminals have been exposed.
In a demonstration of attack vectors, Pen Test Partners used Shodan.io, a search engine for publicly accessible supervisory control and data acquisition systems and IoT-enabled devices. They were easily able to bring up details of satellite communications terminals on vessels connected to the public internet. In some cases, the login screens for these terminals even showed the vessel’s name or provided links to lists of users online at that moment, visible without even needing to enter login details.
With this sort of information, it is possible to track down details of individual crew members, leaving them ripe for phishing attacks, essentially confidence tricks where attackers disguise themselves as a trustworthy entity to obtain sensitive information such as login details or other ways of gaining access to systems.
But even if the login screens do not show this information, they can still prove a vulnerability. Many users do not change the default credentials used to log in, with ‘admin/1234’ being a common username/password combination.
Attackers could even go so far as to track down a specific vessel by using data giving a heading and map co-ordinates accessed via the satellite communications terminal, and then comparing this with easily accessible automatic identification system data to identify a vessel. Even in a busy port or shipping channel it can be possible to single out a particular vessel using this means.

Snapshot CV: Peter Broadhurst
Peter Broadhurst has spent more than 25 years in technical sales, marketing and management in maritime. This inlcudes various roles at antenna manufacturer Sea Tel and director of stabilised antennas at Cobham Satcom. He joined Inmarsat in 2014 as vice president of maritime and took over his current position as senior vice president for safety and security services in 2016.
Related to this Story
Events
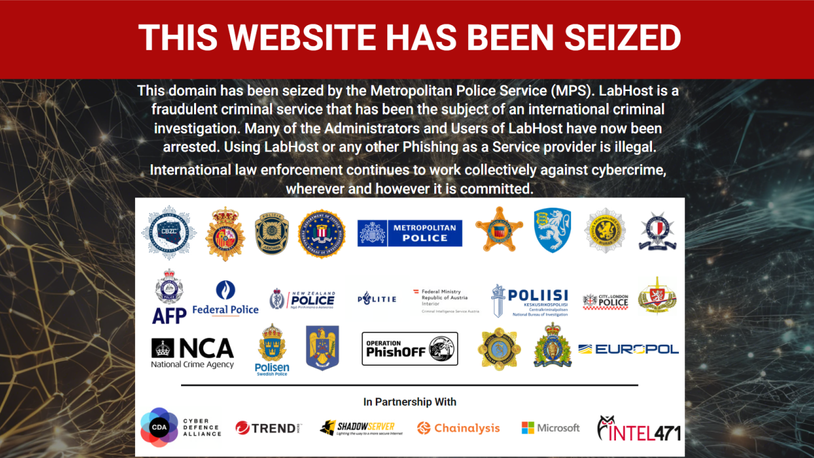
Maritime Cyber Security Webinar Week
Marine Propulsion: Fuels Webinar Week
How enhanced connectivity is propelling maritime into the AI era
Marine Lubricants Webinar Week
© 2023 Riviera Maritime Media Ltd.