Business Sectors
Events
Contents
IMO should ensure security covers all shipboard systems
The maritime industry’s approach to cyber security must cover all shipboard systems if it is to be effective. IMO and other shipping industry organisations should drive forward with introducing robust certification and approval processes for all electronic equipment on board ships.
According to Transas chief executive Frank Coles, this is the only realistic way of tackling cyber risk and security within the maritime sector. He notes that there has always been a certain degree of risk associated with entrusting computers to perform tasks previously carried out manually.
“This is not a new phenomenon,” he commented. “It has been with us since the 1960s and 1970s since electronic systems escaped the laboratory and found their way into real-life applications.”
The reason the subject comes under intense scrutiny today is that these systems are becoming ever more complex and are increasingly interconnected. “The complexity makes it harder to detect errors that could lead to irrevocable failure,” said Mr Coles. “Greater connectivity allows failures to propagate or cascade through a system and also gives hackers, whatever their motivation, much greater scope to find a weak point of entry into a system. Such is the scale of the problem that, in defence circles, it is a widely held view that the next war will be fought not on the battlefield but in cyberspace.”
Electronics equipment found on ships is traditionally subject to countless prescriptive rules, standards and regulations aimed at ensuring the safety of crew, vessels and their cargoes, as well as the environment. However, not all equipment is treated equally, according to Mr Coles. He added: “There are gaps in this regulatory oversight. The hardware for establishing connectivity between ship and shore is a particularly glaring omission. It is all the more worrying as ships grow more reliant on electronic communications in their operations, especially for safe navigation but also for the ongoing maintenance and upkeep of machinery systems, and to satisfy official and commercial reporting requirements.”
Bridge hardware for certain services has to be designed and built to agreed standards (formulated jointly by authorities and industry) in order to gain certification that allows manufacturers to supply and install it. This includes equipment for the global maritime distress and safety system (GMDSS), the automatic identification system (AIS), the long range identification and tracking (LRIT) system and ecdis.
“Yet, there are no equivalent requirements for antennas, modems and other satellite communications equipment,” said Mr Coles. Each satellite services provider will have a different way of addressing security and cyber risk. Modems, for instance, may be supplied with default passwords. “These are rarely changed or are easy to crack,” Mr Coles continued. “This was the technique employed to great effect by hackers carrying out the Mirai-distributed denial of service attack on internet infrastructure in October 2016. Once known to malicious third parties, this information could be used to disable the antenna.”
This could already have serious repercussions for manned vessels, but for unmanned ships currently under consideration it would be disastrous. Without a hardened communications channel an autonomous ship is unlikely to ever leave port – let alone ply a commercial voyage, said Mr Coles.
“The lack of effective certification for communications equipment has consequences for other equipment,” he comments. “When Transas manufactures an ecdis capable of downloading chart updates over the internet, the router and hardware firewall component is scrutinised in the approval process to ensure we are not leaving the ecdis console and thus mariners exposed to any cyber vulnerability. If we decide to switch to a different router, we have to start all over again.”
This is time consuming and an expensive exercise, with costs ultimately feeding through to the end user. “However, there is no similar obligation on manufacturers of satellite communications hardware,” Mr Coles noted. “In my view, this creates a dangerous gap in the regulatory framework for protecting ships – and one that should be plugged quickly.”
Some communications providers propose cyber security add-ons as part of their offering to shipowners, which are typically filtering solutions. “In my view, this approach addresses symptoms that present themselves at the service level, but not any underlying vulnerabilities found in the infrastructure,” Mr Coles commented. “The complexity of modern software and hardware makes it difficult, if not impossible, to develop components without flaws or to detect malicious insertions. Vulnerabilities could exist right down to the firmware or chip level. The Mirai malware attack in October 2016 was so effective because the default password had been burned into the firmware.”
Mr Coles thinks there is a part to be played by IMO and class societies in improving the cyber security of ship electronics. “It is incumbent on IMO and allied organisations to step up and address this reality,” he suggested. “Furthermore, we have to proceed on the assumption that flaws do exist and take a risk-based approach to ensure that when something goes wrong, we have steps in place to minimise the impact. For this reason, the role of class societies cannot be underestimated. Certification for all electronic equipment will provide a level of assurance to mariners that the equipment they rely on is fit for purpose.
However, Mr Coles thinks certification for manufacturers is only part of the solution. He thinks shipowners, too, have a part to play. “One appeal of a risk-based approach to tackling cyber threats is that it can be implemented at various levels. Shipping companies can self-audit and implement their own internal procedures geared towards securing their computer systems. These should cover operations both on ship and on shore. As with so much in life, we cannot eliminate risk entirely, but we can take steps to minimise exposure to unnecessary risks.”
Related to this Story
Events
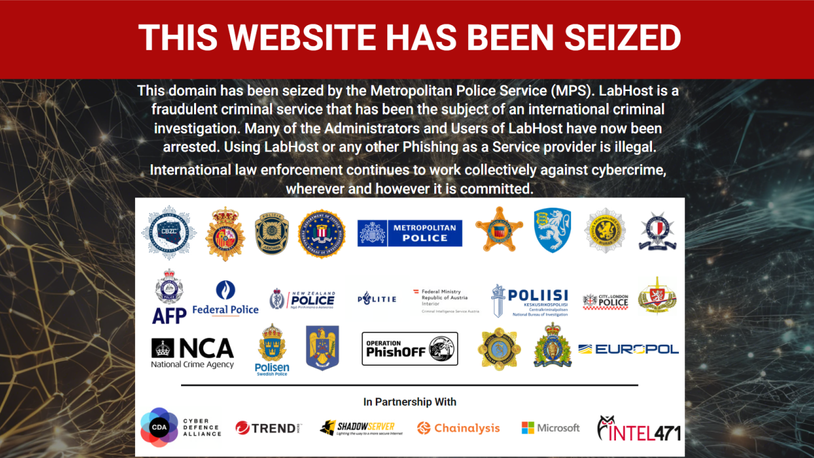
Maritime Cyber Security Webinar Week
International Chemical & Product Tanker Conference 2024
Marine Propulsion: Fuels Webinar Week
How enhanced connectivity is propelling maritime into the AI era
© 2023 Riviera Maritime Media Ltd.