Business Sectors
Events
Contents
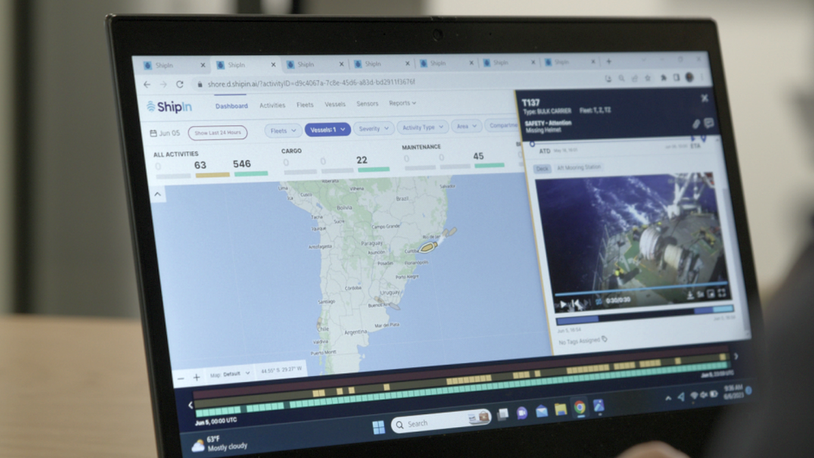
Shipping is not ready for cyber attacks
The shipping industry is unprepared for any serious or lengthy cyber attack. Shipowners, operators and managers may feel they are ready for malware infections on their ships because they employ antivirus software. But they would not be prepared for a well thought out attack from a relentless hacker.
Delegates at the Maritime Cyber Risk Management Summit said they did not think the shipping industry understood the extent of the threats it could face. Around three-quarters of delegates agreed that the industry was not prepared for a comprehensive cyber attack. They voted during an interactive session where PA Consulting security expert Andrew Wadsworth went through the five stages of a cyber attack. Although some delegates felt an intrusion could be contained, the deeper the violation went, the harder they felt this would be.
It was eye-opening to consider how a strong-willed hacker could infiltrate a shipping company in order to reach their objective – to command some aspect of a ship system or onboard equipment. Mr Wadsworth said the first stage of an attack is gathering information on the company and who works within it. Hackers learn the vulnerabilities and begin to get a general picture of where to focus an infiltration.
The second stage is targeting individuals to engineer a benign route into a company’s network. The third stage uses this initial approach to install malware on a company’s network that can capture IP addresses, user names and passwords, and get through company firewalls. The fourth stage is where the hacker can begin to do serious damage to a shipping company’s network. But if the ultimate goal is to penetrate further than this, then the hacker can retrieve more user information and credentials ready for the final assault.
This fifth stage could involve targeting a ship’s network, over the firewalls, without any impediment as the move comes from within the company’s network. Once on the ship network, the hacker could access navigation, automation or dynamic positioning systems.
If this seems unlikely or exaggerated – think again! In an actual case in the second half of 2015, a hacker reached the control systems of a remotely operated vehicle (ROV) on an offshore support vessel. The hacker was able to send a command to the ROV, telling it to ignore any other commands from the onboard controllers. The ROV stopped working and sank to the sea bed, resulting in a US$500,000 salvage operation. The vessel owner had not detected any intrusion and was not prepared for the aftermath. Apparently, the company is not alone in this as the majority of shipping companies would be unaware of any hacking of this nature.
Related to this Story
Events
Maritime Cyber Security Webinar Week
Marine Propulsion: Fuels Webinar Week
How enhanced connectivity is propelling maritime into the AI era
Marine Lubricants Webinar Week
© 2023 Riviera Maritime Media Ltd.