Business Sectors
Contents
Act now to protect fleets and businesses
Operators and managers need to prepare security for cyber threats, and not just to comply with IMO’s upcoming requirements
Ship operators and owners need to prepare for IMO’s changes to the International Ship Management (ISM) Code that sees cyber risk management become part of vessel safety and security plans.
Owners need to act before these recommendations come into force on 1 January 2020, for in four months’ time, port state control such as the US Coast Guard could begin detaining ships for non-compliance. But shipping companies are already being hacked and suffering cyber attacks.
This includes the now notorious attack on Maersk Line’s IT networks in 2017, which caused more than US$300M in losses for the Danish container shipping group. Other more recent attacks include successful cyber breaches on networks operated by Toll Group, Mediterranean Shipping Company, Anglo-Eastern and OSM Maritime Group.
Which is why operators are being urged to invest in cyber security and training for seafarers and shore staff.
These were some of the key conclusions from Riviera Maritime Media’s Cyber security: readying for the ISM Code’s 1 Jan 2021 requirements webinar. This was held on 5 August in association with premier partner ClassNK and sponsor F-Secure as part of Riviera’s Maritime Cyber Security Webinar Week.
During that webinar, ClassNK cyber security team deputy manager Makiko Tani outlined the reasons for shipowners to implement cyber risk management and bolster security.
“Ships today are increasingly leveraging cyber space and operational technology (OT) is more connected with IT and communications,” said Ms Tani. “All this is in pursuit of innovation for fuel efficiency and voyage optimisation, but these bring new vulnerabilities.”
She therefore expects shipowners, operators and managers to ensure cyber risk management is completed ready for ISM Code 2021 and risk assessments are completed within companies and on board ships.
Ms Tani said cyber security “should not just be about compliance” but could open “new opportunities for business and new innovations”.
She said owners with existing fleets should understand the OT on ships and the required cyber risk controls. “Know how your ships are designed and protected,” Ms Tani said. “Be aware of the onboard OT and IT, and where these meet.”
“Can a cyber attack get into the OT?” she asked, adding this could occur through transferring malware, if crew plug their mobile devices into the ship’s ECDIS to charge.
“Compliance to the ISM Code 2021 can start here, by training people and empowering decision makers,” said Ms Tani. She suggested using multi-layered approach for controlling onboard cyber security, which includes updating firewalls, implementing software upgrades and updating antivirus protection. It is also about preventing seafarers from opening email attachments or using unconfirmed links.
There is plenty of guidance for shipping companies. ClassNK has published Guidelines for Designing Cyber Security Onboard Ships, with a second edition published in July 2020. It is applicable to deploying cyber security on newbuildings and is the responsibility of shipbuilders and OT/IT system integrators. This comes with ClassNK’s cyber security notation and is aligned with International Electrotechnical Commission (IEC) 62443 standard and ClassNK’s recommendation 166 on cyber resilience.
In April 2019, ClassNK published its first edition of Guidelines Cyber Security Management Systems Onboard Ships for shipowners and operators responsible for establishing cyber security management systems. It is aligned with International Organisation for Standardisation (ISO) standards ISO 27001 and ISO 27002.
Another applicable document is ClassNK’s Guidelines Ships for Software Security, published in May 2019 for those responsible for establishing cyber security management systems.
Moran Cyber managing director Captain Alex Soukhanov agreed there were more vulnerabilities on modern ships with integrated IT with OT. “Digitalisation is the direction of the industry, so we have to develop continuous and holistic strategies to protect these investments, life, and the environment,” he said. This includes vessel control systems, navigation bridges, engineroom controls and ship automation.
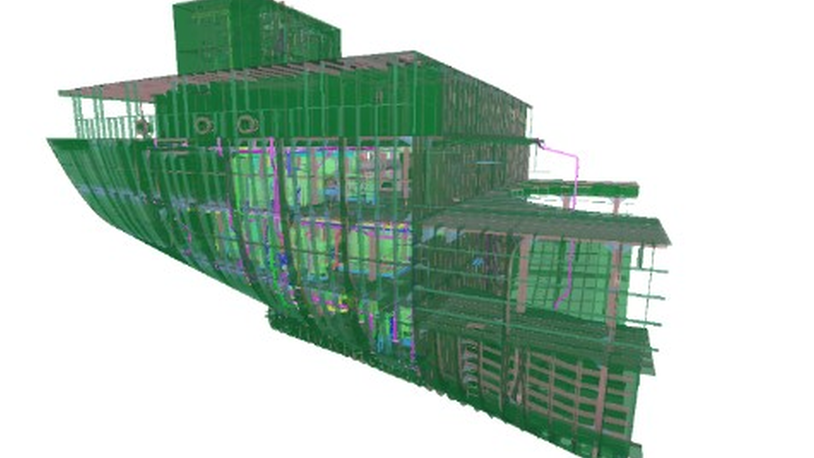
Capt Soukhanov provided a case study within his presentation. This assessed a ship’s OT systems for any cyber security issues. “Our customer required assistance in performing asset discovery of marine OT systems followed by network segmentation from untrusted systems across the fleet,” he said. “We established trust with captains and chief engineers to perform assessments and passive network asset discovery.”
Network segmentation was implemented, and crew were trained on cyber risks and safely operating systems. The results were reduced vulnerable surfaces to cyber threats, increased asset visibility, separating critical OT equipment from untrusted or semi-trusted assets and business protection.
Security by design
Cyber security should be incorporated into ships as they are designed and built, instead of being retrofitted on to ships either for the ISM Code 2021 or as OT is upgraded.
“As digitalisation accelerates, we need to build in cyber security from the start,” said Capt Soukhanov. “Otherwise we are just catching up. Cyber security should be there before the keel is laid.” He said carrying out comprehensive cyber security risk assessments during design will improve safety, resiliency, and reliability through security by design.
Involve vendors during the early stages and extend this collaboration through the lifecycle of investment. Ship operators and vendors “should collaborate and work together to protect onboard systems” said Capt Soukhanov.
Assurance and insurance
Implementing cyber security and risk mitigation is as an opportunity for shipping companies to gain a better understanding of onboard OT and IT, said Beazley senior risk manager Kelly Malynn.
Conducting risk assessments will give owners a better understanding of the cyber threats and vulnerabilities on ships. “Risk assessment quality is important. Owners need to invest in this,” she said. To mitigate risk, segregating networks into subnetworks “makes it harder for an adversary to gain access to essential systems and equipment,” she continued.
“Eliminate the use of generic log-in credentials for multiple personnel. Create network profiles for each employee and require them to enter a password and/or insert an ID card to log on to onboard equipment,” Ms Malynn recommended.
“Limit access and privileges to only those levels necessary to allow each user to do their job. Administrator accounts should be used sparingly and only when necessary. All employees in shipping companies should be wary of external media, stop transferring data via USB drives.
“It is critical external media is scanned for malware on a standalone system before being plugged into any shipboard network. Never run executable media from an untrusted source,” warned Ms Malynn. Basic cyber hygiene can stop incidents before they impact operations. “Install and routinely update basic antivirus software, and do not forget to patch. This is the core of cyber hygiene.”
Ship operators also need to prepare for potential losses and recovery as a successful cyber attack is inevitable. “It is time to reach out to those people with experience – there is insurance cover out there,” she said.
Watch ’Cyber security: readying for the ISM Code’s 1 Jan 2021 requirements’ webinar in our webinar library
Related to this Story
Connectivity propels maritime into the AI era
Events
Shuttle Tanker Webinar Week
International Tug & Salvage Convention, Exhibition & Awards 2024
Responsible Ship Recycling Forum 2024
Offshore Support Journal Conference, Americas 2024
© 2023 Riviera Maritime Media Ltd.