Business Sectors
Events
Contents
Security flaws open ECDIS to cyber crime
Pen Test Partners were able to penetrate leading ECDIS models swiftly and easily simulating what real hackers could achieve
In June, Pen Test Partners were tasked with penetrating multiple makes and models of ECDIS and the results in their own words were shocking. The ethical hackers found high level issues in most ECDIS tested.
Pen Test Partners senior partner and ethical hacker Ken Munro said the most significant issue was that most ECDIS ran on very old Microsoft operating systems, including Windows XP, 7 and Windows NT. This means the majority of ECDIS are not supported by Microsoft and thus, do not have regularly updated security.
“It was therefore trivially easy to completely compromise every ECDIS,” said Mr Munro. “Complete control could be gained over the network interfaces and USB,” he told Marine Electronics & Communications.
Even if the host operating system was up-to-date and secure, most ECDIS offered network services that were vulnerable. These were usually present to allow communication with other operational technology on a ship’s bridge.
Pen Test Partners found exposed configuration interfaces over these networks. “We could boot up the ECDIS from a USB key, locate the encrypted passwords for these services, crack them and then reconfigure the ECDIS,” said Mr Munro.
In addition, the penetrators discovered that these passwords were rarely changed and in many cases, the vendors’ documentation made no mention of changing network service passwords, just the host operating system passwords.
They were also able to cause issues with ECDIS models by sending unexpected network traffic. “In some cases, this led to remote-code execution, whereby we could compromise the ECDIS even if the software was up-to-date,” said Mr Munro.
“We could compromise the ECDIS even if the software was up-to-date”
Some ECDIS models had integrated security software, such as antivirus and firewalls. These were effective for what Mr Munro called “low-grade attacks” but made little difference to higher skill attackers. “We found significant security flaws in the ECDIS software itself, which allowed us to bypass the security software,” he explained.
GPS spoofing
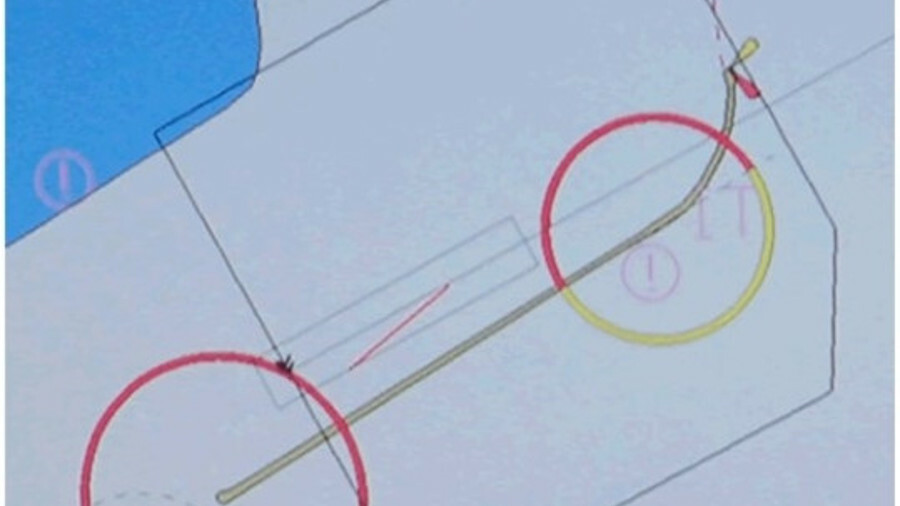
Cyber attacks on ECDIS may not be a direct penetration. Mr Munro’s team were also able to reconfigure ECDIS to believe its GPS receiver was at the other end of the vessel, therefore introducing a 300 m offset.
“Then, through further reconfiguration, we changed the profile of the vessel to be 1 km2 square, for an offset of 1,000 m,” he said. Even further offsets could be introduced by tampering with the US National Marine Electronics Association 0183 serial data being sent to the ECDIS from the GPS receiver.
“Having compromised the ECDIS, we had control over the serial COM ports through which the GPS communicated its position and could tamper with that position data also,” said Mr Munro. Identical offsets could be introduced to radar, meaning a watch officer could not use that method to check for position discrepancies.
Pen Test Partners also demonstrated that automatic identification system (AIS) information could be tampered with. For example, a hacker could create a 1 km2 floating island in a shipping lane. “Every ship ECDIS would be alerted to the phantom blockage and collision potential,” Mr Munro said.
This could cause confusion on ship bridges and potential course alterations that in congested waters could lead to collisions. Hackers could use these techniques to steal money, manipulate ship movements for financial gain or cause vessel groundings or collisions, said Mr Munro.
ECDIS security issues
- Out-of-date software.
- Insecure configuration interfaces.
- Unstable network stacks.
- Vulnerabilities in software.
- GPS spoofing and jamming.
- ENC denial.
- False AIS.
Related to this Story
Events
Maritime Cyber Security Webinar Week
International Chemical & Product Tanker Conference 2024
Marine Propulsion: Fuels Webinar Week
How enhanced connectivity is propelling maritime into the AI era
© 2023 Riviera Maritime Media Ltd.