Business Sectors
Events
Contents
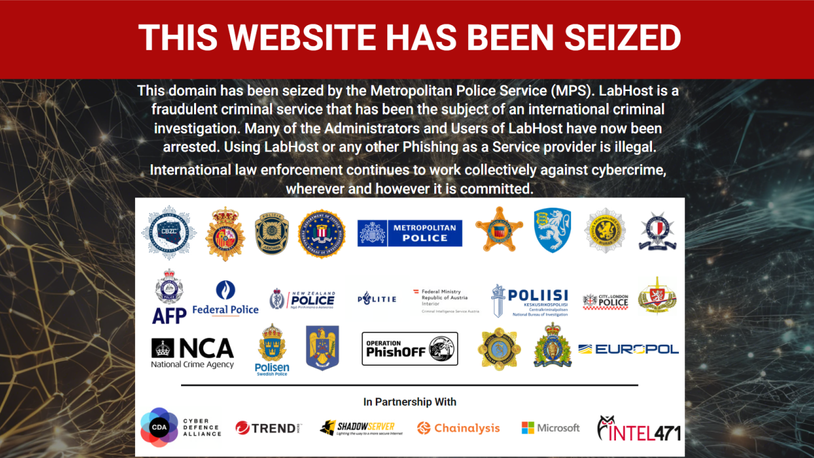
Sophisticated cyber threats make contingency planning as vital as prevention
The threat of suffering collateral damage from state-backed cyber warfare is a matter of when, not if, for shipowners
The threat of suffering collateral damage from state-backed cyber warfare is a matter of when, not if, for shipowners
AP Møller-Maersk was perhaps the highest-profile casualty of the 2017 NotPetya malware attack, with a negative impact on the company’s revenue to the tune of nearly US$250M.
Chief information security officer Andy Powell spoke about how Maersk has implemented the lessons it learned as a result of this at the Maritime Cyber Risk Management Forum in London on 25 June.
“The state-sponsored investment in some of these weapons is beyond the capability even of global companies like ours to defeat [and] you will not stop every attack,” he said.
“What you have to develop is your ability to respond,” he added, noting that the maritime sector excels at such contingency management, and planning what to do should an attack succeed in getting through, rather than focusing solely on prevention, is essential.
Communication is a key element of this, Mr Powell noted. Maersk prioritised informing customers of what had happened openly. While in the short-term this impacted Maersk’s share price, this recovered and customers appreciated the company’s transparency.
He noted that even if conventional communications systems, such as IP-based phones, are put out of action, there are other avenues of communication that can be leveraged. Social media such as WhatsApp played a key role in Maersk’s recovery, with groups being set up within minutes to enable the company to continue to function. Aspects of Maersk’s contingency planning are now based around making use of such tools, Mr Powell said.
He added that using online-based backup is no guarantee of security as this too can be targeted in attacks. “There is no such thing as online backup any more, offline backup and a regime to ensure offline backups work is absolutely critical.”
The only reason Maersk was able to recover was due to having an offline backup in place in Lagos due to Nigeria suffering power outages. “We were lucky,” Mr Powell added, noting that this backup enabled the company’s systems to be back up and running in nine days.
Lost revenue, extraordinary operational costs and expenditure on additional IT capabilities required to rebuild endpoints from scratch all formed part of the financial impact, and while the final figure may seem small in comparison to Maersk’s annual turnover, there were fears the costs could have been much greater, said Mr Powell. He added “At one point during those nine days, it was an extinction-level event.”
In total, more than 40,000 endpoints were taken out, along with 3,000 servers and more than 1,000 applications rendered totally unrecoverable, he said.
While he declined to comment on whether the company’s cyber insurance paid out, Mr Powell emphasised the need to be aware of what cyber cover does and does not cover, noting “A force majeur-type attack, which this was, is a very difficult thing to justify.”
“The collateral damage from a state-sponsored attack can hit anybody,” said Mr Powell. Chinese, Russian and Iranian state actors are all developing weapons that may be intended to target governments but can have a wider impact, and this is a growing trend, he added. He also highlighted that weapons are increasingly using several attack vectors, which is particularly relevant given the increasing levels of digitalisation and OT in maritime.
“What I would like to see in maritime is what we have learned being applied across the sector,” said Mr Powell, emphasising five key operating principles Maersk implemented in the wake of the attack:
- Security is everyone’s responsibility, not just the cyber security team.
- Where business is impacted, appropriate risk accountability is needed.
- Trust is key and customers want to know their data is safe.
- Resilience is a watchword, not just as it relates to technology but also to people.
- Cyber security is a benefit not a burden – every change a company makes has a cyber security implication and by addressing this early, crises further down the road can be averted.
How to implement an effective approach to cyber risk management
Seven lessons must be learned and five key actions taken to formulate and implement an effective cyber risk-management strategy, according to Cobweb Cyber chief executive Michael Hawthorne OBE.
Mr Hawthorne, a former UK defence cyber operations chief and Royal Navy captain, shared his views on cyber risk management and compliance at the Maritime Cyber Risk Forum.
With high levels of connectivity in shipping, when we talk about risk on board vessels we are really talking about risk for the whole company, Mr Hawthorne said.
However, there are two interesting dynamics to consider about ships in terms of risk, he added. “Firstly, they are mobile and not always connected to your network.
“Secondly, the tendency of crews to be shifting all the time [means] the responsibility and accountability for looking after those networks is not the same as it would be for a land-based organisation.”
Seven lessons to learn:
- Leadership: Strong leadership is needed to implement cyber compliance and risk management.
- Governance: Ensure articulation of roles and responsibilities throughout the organisation through effective governance, taking a holistic perspective.
- Identify critical assets: Not everything can be defended so identify the most vital systems in an organisation and prioritise efforts around these.
- Risk management: Organisational processes need risk management embedded within them, incorporating the impact on the wider business as well as cyber security.
- Resilience: Assume that systems will go down and plan how to handle that and get operations up and running, building resilience into this process, rather than focusing purely on preventing incidents in the first place.
- Monitoring: The whole network needs to be monitored, not just endpoints, and someone needs to review this monitoring.
- Incident response: Testing out processes through incident response exercises is vital to practicing risk-management processes and understanding where weaknesses lie.
Cyber awareness is also vital, but these seven processes must be implemented first, added Mr Hawthorne. He also discussed the range of cyber security guidelines available, noting that not all of them are applicable or relevant to every operator. Mr Hawthorne advised evaluating each guideline in light of the requirements of an operators’ area of activity and making a selection based on this. And while there is a wide array of potential frameworks to be implemented, identifying which is applicable requires a similar process, he added.
Mr Hawthorne concluded by outlining five actions for shipowners to take once they are confident the seven lessons have been learned:
- Review your requirements.
- Select your security framework.
- Develop your strategy.
- Allocate sufficient resources.
- Test your security posture and risk appetite.
Related to this Story
Events
Maritime Cyber Security Webinar Week
International Chemical & Product Tanker Conference 2024
Marine Propulsion: Fuels Webinar Week
How enhanced connectivity is propelling maritime into the AI era
© 2023 Riviera Maritime Media Ltd.