Business Sectors
Business Sectors
Events
Contents
Register to read more articles.
Segregate connectivity networks to mitigate cyber risk
Operators of ferries and cruise ships should isolate passenger, business and operational networks, train crew and act on threat intelligence
Passenger ships face a uniquely broad cyber risk profile because they combine transport, hospitality and consumer data environments.
Cybersecurity concerns for ferries and cruise ships include the hacking of critical navigation and propulsion systems, ransomware attacks disabling operations and onboard services, and the theft of passengers’ personal data.
The increasing connectivity of passenger vessels, along with vulnerabilities in terms of onboard wifi, increase the risk of cyber attacks on guests and crew, while dependency on vulnerable satellite communications raises risks for operational security and safety.
“The most immediate exposure comes from passenger and crew connectivity,” said Marlink president for maritime, Tore Morten Olsen,
“Thousands of personal devices create a large and constantly changing attack surface, which is why strict separation between guest networks and operational or business systems is essential,” he explained.
Disruption to the onboard accommodation environment is another major risk for ferries and cruise ships operating worldwide.
“Systems supporting retail, catering, excursions and passenger services are directly tied to revenue and experience and can be targets for phishing and credential-based attacks,” said Mr Olsen. “Any compromise in these systems is immediately visible and reputationally damaging.”
Cyber incidents affecting navigation or machinery systems can become safety events, which is why IMO guidance requires cyber risks to be managed within the ship’s safety framework.
The potential consequences of a security breach could include loss of propulsion, corrupted positioning data or failure of critical onboard systems.
“The shipping industry increasingly recognises that cyber risk must be treated alongside traditional maritime safety risks, not as a separate IT concern,” said Mr Olsen.
IMO sets out the main regulatory requirements for passenger ships, including maritime cyber frameworks, through its maritime safety and facilitation committees.
“Any compromise in these systems is immediately visible and reputationally damaging”
The International Association of Classification Societies (IACS) set unified requirements E26 and E27 for cyber-resilient ships and onboard bridge systems.
There are national frameworks, including US Coast Guard rules, which raise expectations around cyber resilience across IT and operational technology and the European Union’s NIS2 directive, which introduces stricter requirements for data protection, risk management and incident reporting, with penalties for non-compliance.
“The challenge for passenger ship operators is cumulative and global,” said Mr Olsen. “They must align maritime safety regulations, class requirements and data protection laws while operating across multiple jurisdictions in a continuously evolving compliance environment.”
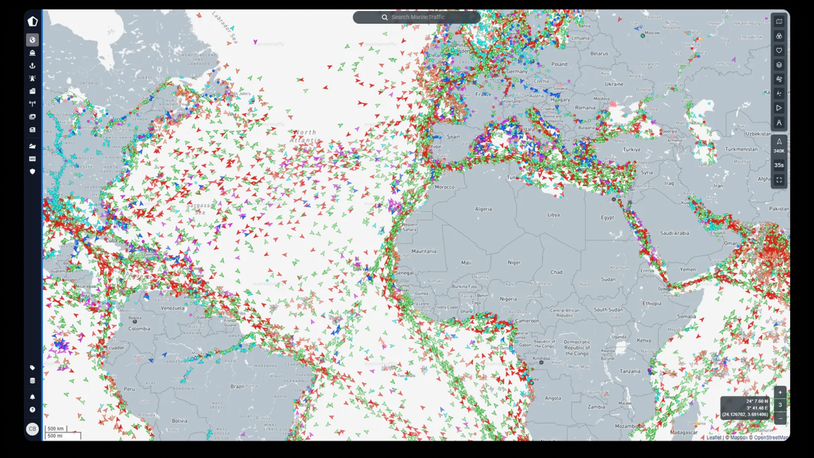
The main vulnerabilities on passenger ships are those connected to online services or when using a Global Navigation Satellite System (GNSS) – such as GPS, Galileo, Glonass, and BeiDou – for positioning, navigation and timing information.
“The primary vulnerability is the convergence of multiple digital environments on board,” said Mr Olsen. “Passenger connectivity, hotel systems, corporate IT and operational technology all coexist, increasing the risk of lateral movement if segmentation is not robust,” he said.
Passenger networks are difficult to control due to privacy constraints, so operators rely heavily on strong segregation and monitoring of non-passenger systems.
“There is also exposure through complex supplier ecosystems supporting onboard services, as well as the sector’s high visibility,” Mr Olsen added.
“Cruise ships are prominent, consumer-facing assets, which makes them attractive targets for disruption or reputational attacks.”
The main cybersecurity solutions for ferries and cruise ships involve strict network segmentation to isolate passenger, business and operational networks and heightened crew awareness of potential security breaches.
“On top of that, the focus is on continuous detection and validation,” said Mr Olsen.
This includes extended detection and response, vulnerability scanning, penetration testing and external attack surface management.
Operators need to maintain operational cyber capabilities to monitor systems 24/7 and respond to incidents and threat intelligence, enabling continuous cyber risk management across fleets.
Threat intelligence comes from maritime information-sharing communities, such as Norma Cyber, that help operators anticipate and respond to sector-specific cyber threats.
“These capabilities are delivered as part of an integrated, managed environment, rather than standalone tools,” said Mr Olsen.
“By combining connectivity, network control and cyber security within a single operational framework, operators gain visibility and control across ship and shore, supporting both safety-critical systems and the passenger experience.”
Sign up for Riviera’s series of technical and operational webinars and conferences:
- Register to attend by visiting our events page.
- Watch recordings from all of our webinars in the webinar library.
Related to this Story
Events
Maritime Regulations Webinar Week
Floating energy: successfully unlocking stranded gas using FLNGs and FSRUs
© 2026 Riviera Maritime Media Ltd.